SSL Certificate
Deploy an SSL certificate to enable HTTPS encryption of websites, trusted identity authentication and prevent against data leaks or tampering during transmission.
Get SSL Certificate >Verify the organization identity
iKey USB token
Unlimited signatures
Display organization, department or group signature
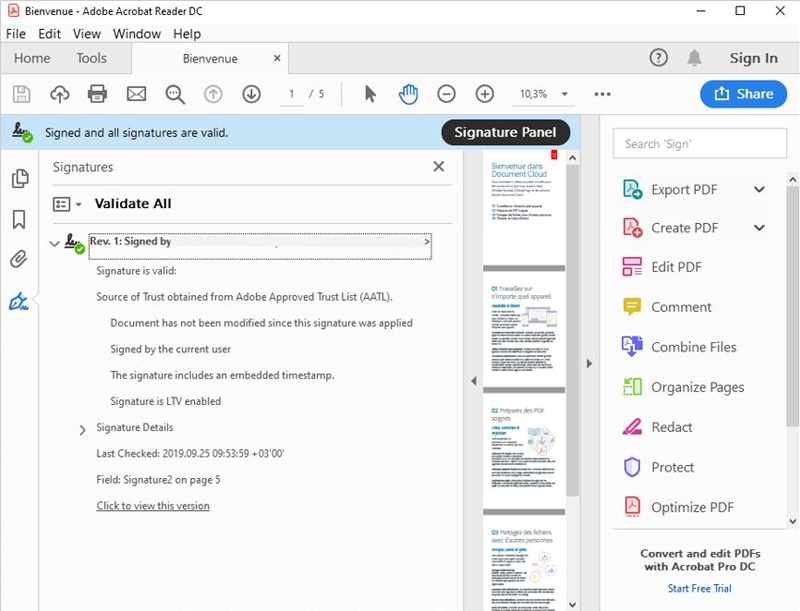
All document signing certificates Root certificate have been entered into the root Adobe and Microsoft root certificate library trust lists, which means that document signatures are fully recognized and trusted, and support global use.
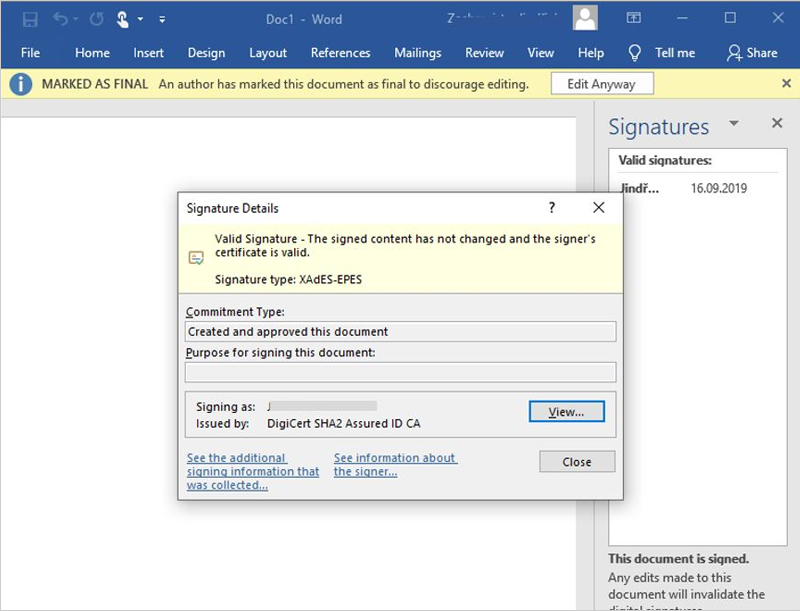
When a digitally signed document is modified, an "X" will be printed at the signature area to remind the user that the document has been modified after signing, ensuring the integrity, authenticity, and legality of the document.
Support all mobile platforms, Adobe series products (such as Adobe Reader, Adobe Acrobat) in various operating systems both domestically and internationally, and Office series products (such as Word, Excel, PowerPoint, Office365, and Microsoft Online Office platform) for document signature formats.
The private key of the document signing certificate is stored in a UKey or encryption machine, providing a high level of security protection for the certificate while also possessing the characteristics of convenience and time saving.
The document signature certificate meets the legal and regulatory requirements for electronic document signing in multiple countries and industries, including the Electronic Signature Law, HIPAA, FDA, eIDAS, ESIGN and UETA in the United States, and the United Nations Model Electronic Signature Law. It has legal effect in some countries such as Europe and America.
By using a timestamp, even if the certificate originally used for signing has expired, the signed document signature will never expire. If someone modifies the signed document after the original signing certificate expires, the digital signature will still prompt that the document has been modified.

Financial institutions have a large number of paper documents (such as investment contracts, insurance agreements, bank statements) that can be signed using document signature certificates to ensure that electronic document signatures comply with relevant laws and regulatory review requirements, ensuring their authenticity, validity, legality, and compliance.

Document signature certificates can reduce the number of paper documents used by government related institutions, help to achieve office automation, Paperless office, reduce government costs, and improve the convenience of public access to government information.

Document signature certificates that meet the requirements of FDA regulations can help a large number of medical documents, such as medical records and prescriptions, become electronic. Digitally signed medical documents are not only easy to manage, but also have Tamper resistance and non repudiation, which can provide legal basis for medical disputes.

The document signature certificate can seamlessly switch the industry's paper-based document business workflow to the Paperless office electronic business workflow, making the entire process efficient and labor-saving, while also ensuring that documents will not be illegally tampered with and authentic during transmission.

Legal cases involve a large and important amount of confidential information, and when transmitting documents, their convenience and confidentiality are the most important factors that law firms value. The document signature certificate precisely protects the privacy of legal related electronic documents transmitted.

A large number of student personal information sheets, transcripts, learning materials, and other educational record information need to be digitized. Document signature certificates can be digitally signed on multiple formats such as PDF or Office to help prevent documents from being tampered with during storage and transmission.
Document Signing Certificate is designed to apply in paperless office operations to digitally sign any document. Digital signature doesn't only protect valuable online data, but also makes them enjoy the efficiency of e-document workflows.
Document signing certificate can authenticate sender's identity and the recipient also can review a trusted digital signature on the document. It assures authenticity of the document.
Compliant with industry standards, Document Signing Certificate support RSA algorithm, 2048+bit keys, SHA256-bit encryption to protect critical business documents and data from tampering by malicious parties.
Documents signed with the trusted Document Signing certificates comply with the U.S. Federal ESIGN Act, European Union's and eIDAS and other assorted international laws, making your documents legally binding.
Digital signatures created by Document Signing Certificates can be timestamped and include an audit trail that never expires. This means if the document is altered at any time, the recipient will be notified immediately.
Sectigo Document Signing certificate offer unlimited signatures in its lifetime. This is an excellent deal if you're signing many documents every year—you won't have to pay for each document you sign.
FAQs on SSL Certificates
A Document Signing Certificate is an electronic file issued by a Certificate Authority (CA). It contains a pair of secure digital key for assuring signer’s identity authentication and integrity of electronically transmitted documents.
Digital signatures, like handwritten signatures, are unique to each signer. It uses public key infrastructure (PKI), which is considered the gold standard for digital identity authentication and encryption. PKI relies on the use of two related keys, a public key and a private key, that together create a key pair to encrypt and decrypt a message using strong public key cryptography algorithms. Using both public and private keys that are generated to provide the signer with their own digital identity, a digital signature is generated and encrypted using that signer’s private key, and also a timestamp of when the document was signed using the key. These keys are normally saved in a secure manner; for example, Sectigo and DigiCert sends USB with your certificate and keys to you.
Validation is an important part of certificate issuing process. As such, every CA has followed stringent validation policies and procedures to strengthen the security of certificate operations and the validation processes. Take Sectigo for example, and this is the validation materials needed below:
The validation work is done by Sectigo. You are required to respond to emails, follow instructions and provide the requested documents.