SSL Certificate
Deploy an SSL certificate to enable HTTPS encryption of websites, trusted identity authentication and prevent against data leaks or tampering during transmission.
Get SSL Certificate >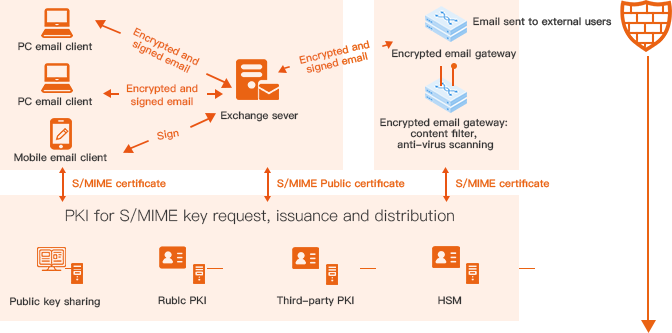
Background
Corporate espionage and espionage between nations have resulted in nearly $30 billion in economic losses. End-to-end email encryption can make email communication more secure.
Architecture Description
Self-developed email encryption solution to meet the ITAI Industry's requirements.
The system flexibly adjusts email message flow and certificate flow to adapt to the existing email architecture of the enterprise.
Supports S/MIME certificates from various CAs, including public CAs (DigiCert, Sectigo, etc.) and private CAs.
Fault tolerance and load balancing for high stability.
Zero-Touch S/MIME issuance and deployment without manual intervention. The automatic certificate issuance and deployment can greatly reduce the cost of issuing and using S/MIME certificates, and reduce error rate as well.
Works seamlessly with DigiCert, Sectigo, Entrust, and NicSRS private CA.
Supports cloud and local escrow backup of S/MIME certificates which can be recovered in case of system reinstalling or employee losing the key to avoid situations where encrypted emails cannot be viewed.
Provides a powerful and automatic platform for public key exchanging. Once the email user submits the public key, all employees in the enterprise can automatically obtain it for encryption. The system can automatically intercept emails without the recipient's public key, and send them automatically after the recipient submits the public key.
Supports enterprise-level S/MIME keys setup between enterprises, so that two enterprises can send encrypted emails to one another without public key exchanging between employees.
Emails will be decrypted temporarily by the scanning gateway, and then be encrypted and sent after they are scanned and approved.
The solution is compatible with all email clients that support S/MIME, and supports custom extension and development of clients as well. Currently, the email clients supported by default include Outlook, Thunderbird and more, and built-in emails on Android, iPhone and HarmonyOS, etc.
No. The email encryption gateway is compatible with existing email security gateways. The encryption gateway will decrypt the email, send it to the email security gateway for content scanning and then re-encrypt it and send it out again. Any of the current mainstream email security gateways can be integrated with the email encryption gateway. You can contact our customer service for more info.
At present, we are compatible with the S/MIME of Sectigo, DigiCert, and Entrust, and S/MIME certificates can be issued according to needs. In addition, we also support S/MIME certificates signed by private CAs. You are also welcome to use NicSRS private CA system. If you are using a third-party private CA, please contact customer service to find out whether it is supported, or customization workload.
Our system is designed so that the sender doesn't need to understand the technology behind when using the encryption function. The email will be intercepted at the gateway, and the encrypted gateway will automatically send an email to the recipient, requesting him/her to submit the public key or view the email on the encrypted gateway.